What is ITDR?
Most businesses today don’t get “hacked” like TV shows and movies often showcase, with someone “hacking into the mainframe”. They, quite simply… get logged into.
Confused? Let’s explain.
This all starts with an employee’s credentials being stolen.
A cybercriminal signs in quietly, looks like a normal user, and starts moving around systems that were never meant to be exposed. By the time anyone notices, the damage is already done.
This is the exact problem ITDR was created to solve.
ITDR, Identity Threat Detection and Response, focuses on protecting the one thing modern cyberattacks rely on most, that being digital identities. Not firewalls. Not endpoints. Identities.
And for business owners, that shift matters more than most realise.
What ITDR Actually Means
At its core, Identity Threat Detection and Response is about three things:
- Watching how identities behave
- Detecting when that behaviour becomes risky or abnormal
- Responding before real damage occurs
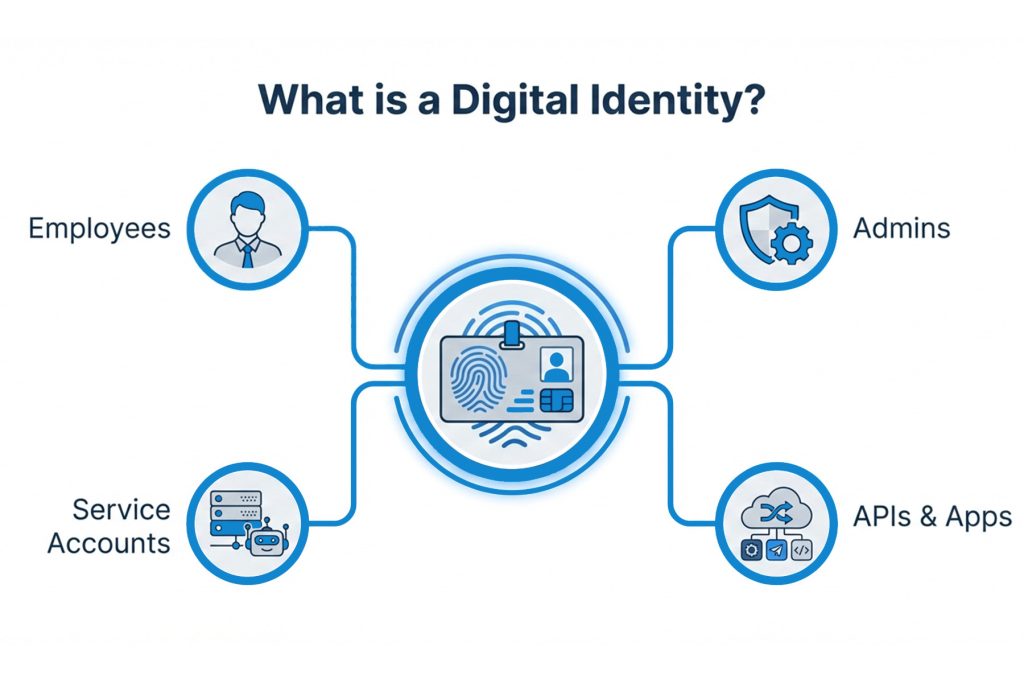
An “identity” here isn’t just a person. It includes:
- Employee accounts
- Administrator accounts
- Service accounts
- Cloud app identities
- API integrations
Identity Threat Detection and Response tools sit across identity platforms like Microsoft Entra ID (Azure AD), Google Workspace, and other identity providers. They continuously analyse login activity, privilege changes, token usage, and access patterns.
When something doesn’t add up, ITDR steps in. Not with generic alerts, but with context-driven intelligence.
Why Cybercriminals Attack Identities over Systems now
Over the past decade, business IT has changed dramatically.
Employees work remotely. Cloud services are everywhere. Email, file storage, accounting systems, CRMs, and line-of-business apps all sit behind logins rather than internal networks.
As a result, cybercriminals have adapted.
Instead of trying to break through hardened perimeters, they aim to steal or abuse identities. Usernames, passwords, MFA tokens, API keys, permissions, anything that lets them authenticate as a legitimate user.
Once they have that, traditional cybersecurity controls often don’t trigger alarms. From the system’s point of view, everything looks normal.
This is why identity-based attacks now sit at the centre of ransomware incidents, data breaches, and business email compromise.
ITDR exists because legacy cybersecurity tools were never designed to monitor identity behaviour at this level.
How ITDR Differs from Traditional Cybersecurity Tools
A common misconception is that ITDR is simply “better multi-factor authentication” or another feature bolted onto a SIEM platform. It isn’t. ITDR was built to solve a different problem than traditional cybersecurity tools were designed for.
Traditional cybersecurity tools focus on infrastructure:
Firewalls inspect network traffic, endpoint tools watch for malicious activity on devices, email security filters suspicious messages, and security information and event management platforms (SIEM) collect logs from across the environment. These tools are essential, but they largely assess systems in isolation.
ITDR focuses on identity behaviour over time:
Consider a typical identity-based attack. A firewall may allow a login because the credentials are valid. The endpoint shows no signs of malware. Multi-factor authentication has already been approved by the user. From a traditional security perspective, nothing appears wrong.
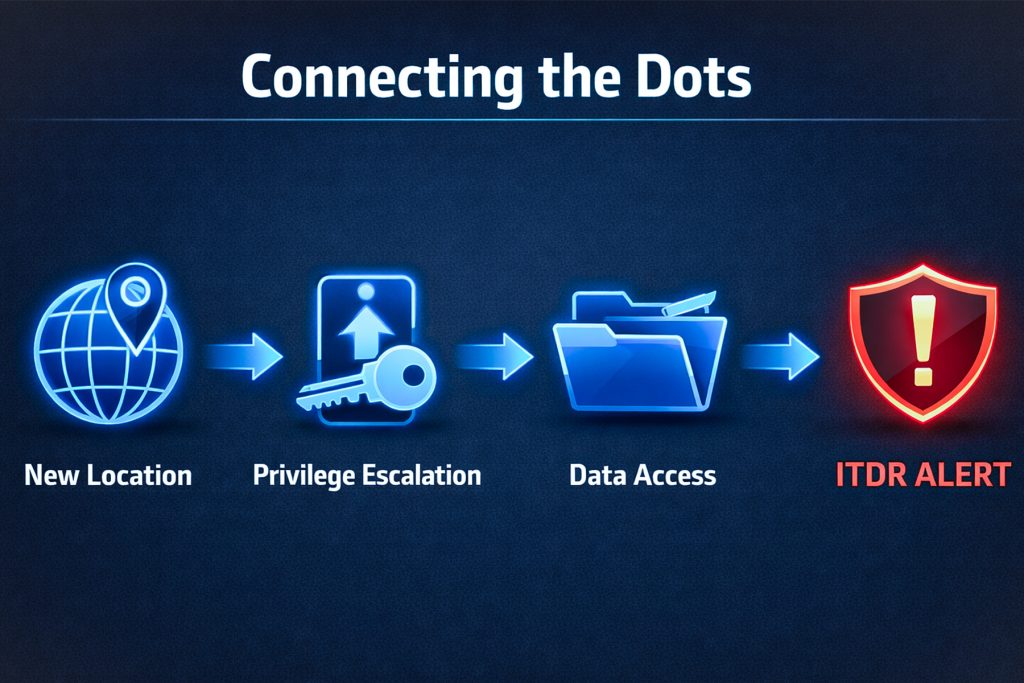
ITDR, however, sees the broader pattern. It may detect that the user logged in from a new country, immediately escalated their privileges, accessed sensitive systems they have never used before, and created new OAuth app permissions to maintain access. Each of these actions, viewed on its own, could have a legitimate explanation. Viewed together, they form a clear indicator of risk.
That ability to connect context across identity activity is what sets ITDR apart. It doesn’t just ask whether an action is allowed, it asks whether it makes sense.
That’s the value of ITDR.
What ITDR is designed to detect
ITDR is particularly effective against attacks that bypass traditional controls. These include:
Credential Misuse: When stolen usernames and passwords are used successfully, especially in combination with MFA fatigue or token theft.
Privilege Escalation: When a standard user suddenly gains admin-level access or modifies role assignments without a clear business reason.
Lateral Movement: When an identity begins accessing systems or data outside its normal scope.
OAuth and API Abuse: One of the most overlooked risks. Attackers increasingly use malicious app permissions to maintain persistence even after passwords are changed.
Insider Threats: Not all threats come from outside. The notifiable data breach statistics for January – June of 2025 show that human error accounted for 37% of all data breaches reported. ITDR can detect risky or negligent behaviour from internal users before it becomes a major incident.
Why ITDR Matters for Business Owners
For businesses, ITDR isn’t about adding another security tool to the stack. It’s about reducing risk where modern cyberattacks actually occur, at the identity level.
When identities are compromised, the consequences are rarely minor. These incidents commonly result in data breaches that trigger regulatory exposure, financial fraud through invoice redirection, ransomware being deployed inside trusted systems, and long-term reputational damage. On top of that comes the cost of incident response, forensic investigations, and recovery efforts that often stretch well beyond the initial attack.
What makes identity-based attacks particularly damaging is how quietly they unfold. Attackers no longer rely on loud, obvious techniques. They sign in, blend into normal activity, and operate unnoticed for extended periods, giving them time to maximise impact.
ITDR changes that equation by dramatically shortening the detection window. Instead of discovering an incident weeks or months later, suspicious identity behaviour is identified early, while it can still be contained.
In practical terms, this means breaches are smaller, response is faster, recovery costs are lower, and business disruption is reduced. For many organisations, ITDR becomes the critical link between identity management and incident response, filling a gap that traditional cybersecurity controls were never designed to address.
How ITDR Fits into Managed IT Services
For most businesses, deploying ITDR effectively isn’t a DIY exercise.
Identity systems are complex. Alerts need tuning. Responses must be automated carefully to avoid business disruption.
This is where Managed IT Services play a critical role.
A managed provider can:
- Integrate ITDR with existing identity platforms
- Define normal behaviour baselines for the business
- Provide continuous monitoring
- Respond to cyber threats in real time
- Align identity security with broader cybersecurity strategy
Instead of reacting to breaches, businesses move toward proactive identity protection. That shift alone can significantly improve overall cybersecurity maturity.
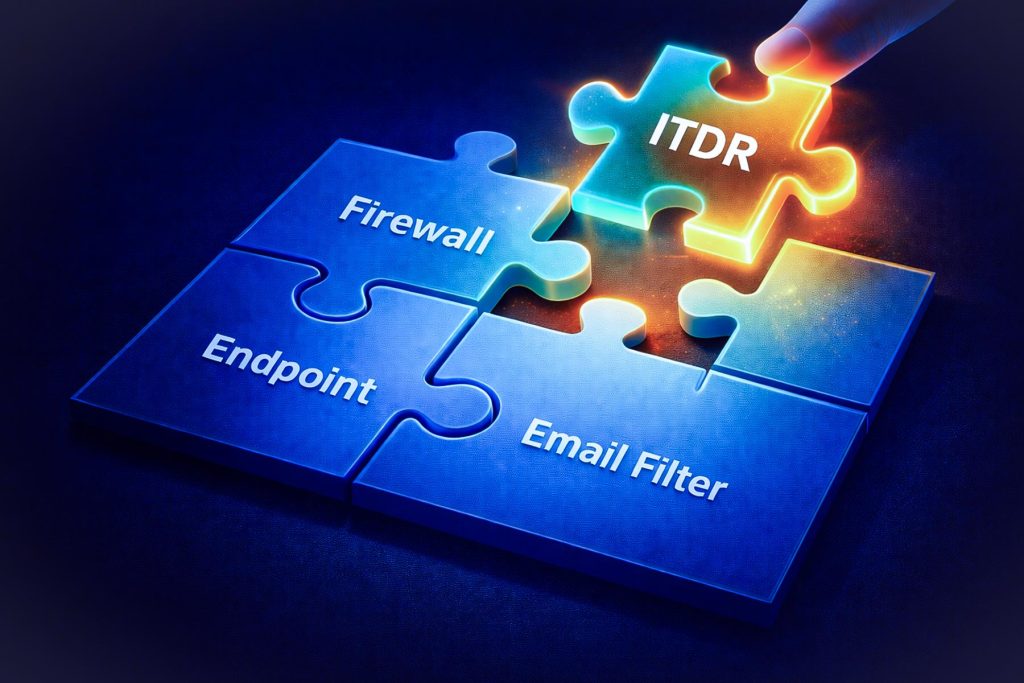
Think of ITDR being the final puzzle piece in your overall cybersecurity standards for your business.
ITDR for your Business in 2026
ITDR isn’t about replacing your existing security stack. It’s about strengthening the weakest and most targeted link in modern business IT, being identities.
Whilst traditional cybersecurity processes and systems still perform adequately, ITDR provides the next level of cybersecurity for businesses heading into 2026 and beyond.
For business owners, that means fewer surprises, lower risk, and stronger protection where it matters most.
If you’re already investing in cybersecurity but haven’t looked closely at identity threat detection, it’s worth a conversation. Not because it’s trendy, but because it reflects how cyberattacks actually happen today.
Adept IT Solutions is here to help with all your ITDR needs! Looking to upgrade your cybersecurity standards, and take your business to the next level? Contact us today!
You can reach us via phone at 1300 423 378 or email us at info@adept-it.com.au.

